| GNSS | |
GNSS disruption – what’s the risk?
A white paper by the Resilient Navigation and Timing Foundation offers some initial answers |
 |
|
GNSS signals are being disrupted all the time. Why should we care?
Those in the GNSS/PNT community will say it’s because virtually every technology uses GNSS signals, and most depend upon them. When signals are disrupted, something bad could happen.
But how likely is that? What is the risk and are we willing to take it? These are questions that many governments are starting to ask.
To understand how this is being done, we must first understand how people think about and calculate risk.
We all calculate risks every day. How likely is a bad thing to happen, am I likely to be affected, and, if so, what will be the impact? Most of the time these calculations are unconscious. Shall I get on an airplane to go to a conference? There could be bad weather, the airplane could crash, I could die. But I think there is little chance of bad weather, and, if there is, the airplane and pilots can handle it, so there is almost no chance I could die. So, even though my dying would be a very, very bad outcome, I buy my ticket without a second thought.
For more complex decisions, risk managers in government and elsewhere make pretty much the same kind of calculations, though they are much more systematic and thorough. They look at risk as the product of three factors as a way to quantify risk:
Threat, defined as the probability of an adverse event (like the weather),
Vulnerability, or how likely the adverse event is to cause harm (affect the airplane), and
Consequence, the harm that could be done (crashing and me dying).
Let’s take a simple, non-aviation, example. If the probability of a category 5 hurricane (adverse event) striking New Orleans in any given year is 25%, and there is a 50% chance the levees will fail (vulnerability) and this will cause $2B in damage (consequence), then the risk to New Orleans from category 5 hurricane can be calculated as:
25% per year Threat x 50% Vulnerability x $2B Consequence = $250M per year Risk
In this case the risk is expressed in dollars. Often though, it is difficult to assign dollar amounts to consequences. In such cases, risk analysis will assign scores to different severities of consequence. This allows the risks associated with a wide variety of adverse events to be scored and evaluated.
The relative risk of several different adverse can then be compared, and the impact and value of different mitigation efforts can be evaluated.
So how does this apply to GNSS disruptions? (We though you would never ask!)
To understand risks associated with GNSS disruptions, we have to know about:
Threats – What are possible GNSS disruptions, and how likely are they to occur?
Vulnerabilities – How likely are each of these adverse events to cause harm to GNSS users?
Consequences – What is the severity of the harm that could be done?
A white paper by the Resilient Navigation and Timing Foundation offers some initial answers to these questions. Note that while the paper addresses just GPS, its methods and findings are generally applicable to all GNSS systems and users.
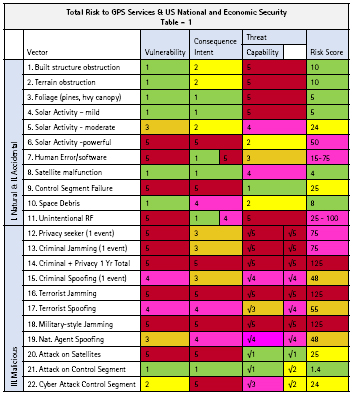
Threats – Surveying professional literature we were able to describe 22 two types of adverse events (we called them “vectors”) that could disrupt GPS services. These ranged from terrain and foliage obstructions and interference from solar activity, to military grade jamming and spoofing.
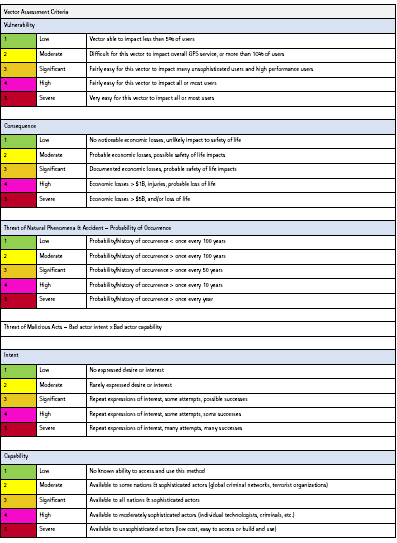
We then estimated on a scale of one to five how likely each adverse event or vector was likely to occur. Very unlikely (happens less than once a century) was scored as “1” and things that happen several times a year were scored as “5”. The probability of malicious acts, like one nation jamming another, was defined as the product of “intent” and “capability” – or “how much they want to do it” multiplied by “how likely they are to be able to make it happen.”
Vulnerability – Since we were looking at the cumulative societal impacts of GNSS disruption, we assessed vulnerability by what percentage of GPS users would be impacted. Very few users, for example are impacted by foliage (vulnerability score of “1”), but most all users would be affected by a massive solar flare that ionized the atmosphere and prevented GPS signals from reaching Earth (vulnerability score “5”).
Consequence – We used a scale that ranged from “1 – No noticeable economic losses, unlikely impact to safety of life” to “5 – Economic Losses > $5B and/or Loss of Life”
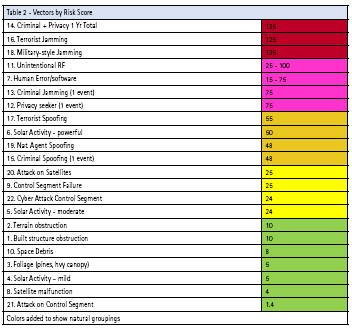
Much of what we found is probably not a surprise to anyone.
Posing the least risk to society were things like built obstructions, foliage, and mild solar activity. Space debris and a single malfunctioning satellite also fell in that category.
The greatest risks were from high powered military and terrorist jamming, and the cumulative effects over the course of a year from wide-spread low power jamming by criminals and privacy seekers. (See table 2).
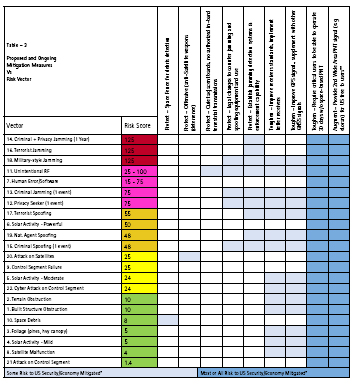
We also took a high-level look at nine different proposed mitigations, or ways to reduce the risk to society, from GPS disruptions. These varied from the US Air Force’s “space fence,” to implementing a high-powered terrestrial complement to GPS and requiring critical infrastructure and applications to be able to survive for 30 days without GPS signals. The space fence seemed to only mitigate one, low risk threat vector, while the terrestrial complement and 30-day mandate seemed to address all the threats and reduce the most risk.
But, of course, our single white paper is not the final answer. In fact, it is really only a methodology that points to questions that must be asked and decisions that must be made.
And some governments are beginning to ask the questions. The European Union is addressing some aspects of the threat. Their STRIKE3 project has found hundreds of thousands of low level GNSS interference events, over 50,000 intentional jamming events, and identified 300 jammer “families.” The United Kingdom has studied consequence and estimated that a five-day GNSS outage would cost the nation at least £5.2B. And South Korea is beginning to implement a mitigation in the form of a terrestrial eLoran system to augment GNSS signals and eliminate their critical dependence on space.
While all of these are good and needed efforts, comprehensive national approachs to protecting GNSS and PNT services seem most appropriate. We believe that every nation needs to simultaneously protect GNSS signals by actively combatting interference, ensure users are toughened with receivers that reject interference as much as possible, and to augment GNSS signals with sovereign terrestrial systems so tht they won’t be dependent upon weak, easily disrupted signals from space.
The good news is nothing really bad in the way of GNSS disruption has happened yet, and some nations are slowly moving to protect themselves. The bad news is that they are moving slowly, while both threats to GNSS signals and their national dependence upon them grow.
Should nations move more quickly? Should we all be worried? Well… what’s the risk?
References
“Prioritizing the Dangers to the United States from Threats to GPS” https:// rntfnd.org/wp-content/uploads/12- 7-Prioritizing-Dangers-to-US-fm- Threats-to-GPS-RNTFoundation.pdf
STRIKE3 http://www.gnss-strike3.eu/
London Economics report – UK impact from GNSS disruption https://www.gov. uk/government/publications/the-economicimpact- on-the-uk-of-a-disruption-to-gnss
South Korea eLoran http://insidegnss. com/ursanav-awarded-contract-tosupply- eloran-transmitter-test-bedsystem- in-the-republic-of-korea/












 (2 votes, average: 4.00 out of 5)
(2 votes, average: 4.00 out of 5)



Leave your response!