| GNSS | |
Cybersecurity in localization
A panel discussion was organized on “Cybersecurity in Localization” at European Navigation Conference held at Helsinki, Finland during 30 May – 2 June 2016. Based on the discussion, we present here some of the opinions |
A cat-and-mouse game of invention and ingenuity
 |
|
GNSS-based localization is no more or less secure today than it was a decade ago. From a technical standpoint, GNSS has always been vulnerable, and the equipment required to compromise it has long been accessible to everyone. Two features of GNSS lead it to be vulnerable: firstly, it is a passive system, based on one-way communication; and, secondly, it is not unusual for it to be sporadically unavailable due either to users being in urban or indoor environments, or temporarily shadowed by buildings or foliage. This said, although it is vulnerable, it has never really been at great risk. As yet, no evidence suggestive of a genuine spoofing attack has been found. Very few average GNSS users are concerned about GNSS security although many are concerned about jamming. However, all this may be changing, as we have recently begun to incentivize malicious behavior.
Over the past decades, being a free global service, GNSS was eagerly adopted by civilians. Those in possession of GNSSenabled devices desired ubiquitous and accurate positioning had a vested interest in their GNSS-enabled device working correctly. Moreover, being interested in the positioning service, they would willingly adapt or intervene in the case of malfunction of the receiver. The naïve principle of operation of the average receiver was shielded by the earnestly motivated user. In the short term, this may be expected to continue. Now we are seeing the beginnings of a very different kind of GNSS application, where the receivers are being employed as tools to assist in monitoring, regulation or penalizing. This has taken the form of road-tolling systems, pay-per-use automotive insurance, geofencing, assettracking and fleet-management. In this situation, the personal interests of the holder or user of the receiver, and the primary function of the receiver itself, are starkly opposed. The possessor of the device is no longer an earnest user of a navigation tool, he is monitored and regulated by this device, and is the very person most interested in compromising it.
Naturally, the more creative and mischievous among us sought ways to disable these monitoring receivers, leading to prevalence of the now infamous cigarette-lighter jammer. Although initially very effective, the persistent use of jammers led to two further developments: authorities learned to localize the perpetrators, and more intelligence was built into the GNSS receiver. A number of governmentinitiated activities across Europe have made progress in the area of spectrum monitoring, interference detection and localization, such that the use of jammers may no longer be an effective strategy for denying localization. Further to this, interference monitoring and mitigation capabilities has begun to appear as a standard feature in massmarket GNSS receivers, which are now equipped to identify, log and report jamming events. The result is that simple brute-force denial of service may no longer be effective. This has raised the bar for the adversary.
Of course, we might expect a proportional response from the cheating user, who will only enhance the jamming device to a sufficient extent, and no more. As such, it is likely that the current jamming threat, as we know it today, will evolve somewhat, striving to successfully deny GNSS-based positioning to a receiver while remaining relatively undetectable or un-localizable. For example, this may take the form of clever pulsed signals, or the use of some form of GNSS-like signals. At some point, however, it is not unreasonable to expect that he will be forced to actively deceive the GNSS receiver: to feed it with synthetic signals corresponding to some other place or time.
The difficulty of successfully deceiving a receiver is heavily dependent upon two factors: one is the a priori level uncertainty of the receiver itself, and the second is the availability of auxiliary sensors and communication channels. The process of deceiving a GNSS receiver may take many forms, and might target one of many interfaces to the receiver including that of the RF chain, the internal memory, receivercontrol, auxiliary sensors, timing or frequency references, AGNSS or correction streams. For typical road-tolling, asset-tracking, fleetmanagement applications, we might expect a simple, low-cost receiver, with limited or sporadic connectivity, and likely in a closed/sealed unit. In this case, the most practical approach to compromising the receiver may be either a synthesis of counterfeit signals, or a relaying/replaying of genuine signals gathered at some other location/time.
Over the past years, quite a lot of work has been done on GNSS spoofing, and a range of possible spoofing attacks have been postulated and even more possible spoofing detection and mitigation strategies have been conceived. Some of these have considered highly augmented receivers, which can avail of multiple antennas, inertial measurement units, odometer, where the receiver will examine features relating to angle-of-arrival and consistency between GNSS and other sensors. Other approaches have considered the case of a well calibrated receiver operating in a benign environment prior to the onset of a spoofing attempts. It is generally assumed that the adversary must dislodge the receiver from the genuine signals and coerce it into tracking the counterfeit ones. In this case the fidelity of the counterfeit signal and the transient behavior of the receiver during the time that the genuine and counterfeit signals interact is the focus of the spoofing detection scheme. In terms of dealing with likely spoofing scenarios in the future, unfortunately neither of these cases are representative.
Examining the likely applications of GNSS which may encourage spoofing, for example road-tolling/automotive insurance or asset-tracking/fleet-management systems, we can imagine a malicious user who has some degree of physical access to the target receiver, perhaps able to shroud the antenna, blocking the genuine GNSS signals, and allowing the introduction of counterfeit signals. In the case that a user were motivated to spoof the receiver, the most effective strategy might be to begin the spoofing operation when the receiver is in a highly uncertain state, for example having had experienced a GNSS outage for a protracted period, and thereby operating a cold- or warm-start acquisition.
Due to their limited resources, singleantenna mass-market receivers, during their cold- or warm-start phase, are quite vulnerable, and are not in a position to exploit many of the established anti-spoofing techniques:
• Without multiple antennas, angleof- arrival based spoofing-detection schemes cannot be used, such that a simple signal generator can be used as a spoofing device. Other approaches, wherein a single GNSS antenna is moved in a prescribed fashion, so as to induce different carrier phase variations on signals arriving from different directions, may also fail. If a spoofer has direct access to the receiver, he may know the antenna movement profile and pre-adjust the spoofed signals appropriately.
• Without inertial sensors, coherency tests between the variation in the GNSS position estimate, and that observed by the inertial measurement unit, may not be possible. Even if low-quality inertial units are available, their initialization or calibration, in terms of bias and scale, is dependent on the prior availability of trustworthy GNSS. As such, although they may be useful for detecting the onset of a spoofing attach when the receiver starts in a safe condition with line-of-signt to the satellites, it may not be useful when the onset of spoofing occurs during cold-start.
• Because it is possible to shroud the antenna, anti-spoofing techniques which search for multiple instances of the same signal, genuine and counterfeit, will not be useful nor will the transient ‘carry-off’ behavior will not occur. The receiver will be presented with and allowed to acquire only one setoff signals, these being the counterfeit ones.
• During the acquisition stage, following a protracted absence of GNSS, it is also likely that the receiver uncertainty of the true time will be very high. This receiver may not perceive that a counterfeit signal is delayed by some tens or hundreds of milliseconds, relative to true time. This uncertainty might allow a spoofer to recover the navigation data carried by the genuine GNSS signals, and subsequently use it in the generation of the counterfeit signals, resulting in counterfeit signals which are bit-for-bit identical to the genuine ones. As a consequence, for these applications, anti-spoofing techniques which operate at the navigation data level, such as cryptographic navigation message authentication schemes (NMA), will not offer any protection.
Securing a cold- or warm-start receiver is challenging, and seems to remain an unsolved problem. Interestingly, very many of the GNSS applications which would benefit from, or even require secured localization, will operate under conditions where the receiver must endure brief or protracted unavailability of GNSS, and subsequently re-acquire all satellites in view. In many cases, the availability of GNSS will be under direct control of the user of the device, for example by shrouding the antenna, leaving the receiver at a distinct disadvantage.
Some means of securing a receiver at during this initial acquisition/reacquisition stage must be found. It is not clear whether this might ever be possible for a stand-alone receiver, if some mechanism or degree of sensitivity to counterfeit signals can be found, or whether some form of duplex connectivity, such as UMTS/ LTE or WiFi, will be required, enabling secure time-transfer and remote signal processing. However, even if a receiver is not absolutely secure, the market will reach an equilibrium, where the cost of compromising GNSS will outweigh the benefit. But, until this happens we are likely to see a cat-and-mouse game of invention and ingenuity.
A cat-and-mouse game of invention and ingenuity
 |
|
Global Navigation Satellite Systems (GNSSs) have become, over the last decade, a pervasive technology which has found applications in different fields, from road transportation to leisure and sport, from spatial analysis of scientific data to safety and regulated applications. The pervasiveness and, sometimes, the invasiveness of this technology along with the economic interests related to the applications it enables have created incentives to disrupt GNSS operation. A clear example is from the road transportation sector where GNSS has promoted the fast deployment of electronic toll collection systems. In this respect, GNSS is the most cost-effective approach for building and expanding a road tolling network with the lowest requirements in terms of infrastructures. A malicious user could be definitely interested in interfering with GNSS operations to reduce or avoid tolling.
Privacy protection has also been often used as a reason for justifying improper behaviors possibly disrupting GNSS signal reception.
Irrespective of the cause, GNSS receivers, as key elements for the fruition of GNSS location-based services, are vulnerable to several forms of cyber-attack. The most known are jamming and spoofing. Jamming is a common reality and jamming attacks have been recorded in several occasions: from the truck driver using a jammer to avoid to be tracked by his employer to the “state-based” jamming perpetrated by North Korea to the detriment of their Southern neighbours. Spoofing is moving from the “research” to the “deployment” phase. Just a few years ago, spoofing was demonstrated only in labs and it is now object of interest of hackers. Attacks and defences will somehow progress in a parallel way Although spoofing may, for the moment, be found too complex or too expensive to have a sufficient incentive to perpetrate it, other options are at the disposal of the malicious user. A cyber-threat which has been probably underestimated till recently is the so called “GNSS data faking” problem or simply “faking”. In this case, the signals at the antenna of the GNSS receiver are genuine, what have been falsified are the output data provided by the receiver itself. The final result is very similar to that achieved by a spoofing attack: false Position Velocity and Time (PVT) are provided to the application using GNSS data.
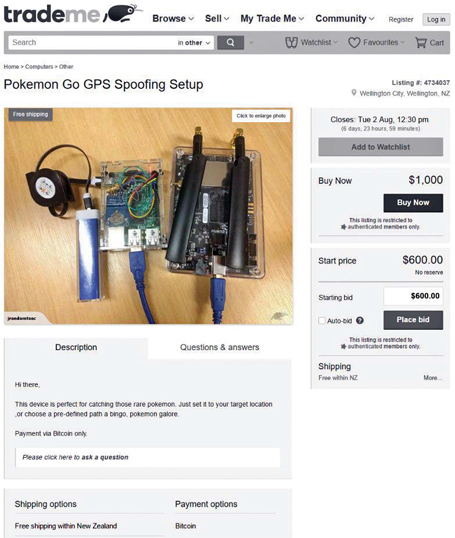
The risks connected to data faking have been strongly reminded to the public by the Pokemon Go game which exploits the location data provided by the GNSS receiver integrated within a smartphone. Pokemon Go players may find an advantage in faking (and sometimes spoofing) the GNSS receiver inside their phone. The Pokemon game resulted, somehow, the right incentive to perpetrate “innocent” cyber-attacks to GNSS receivers.
The lack of awareness of the possible consequences of jamming, spoofing and faking also plays a significant role in the proliferation and development of new forms of GNSS cyber-attacks. Data faking perpetrated for the Pokemon Go case may seem without consequences (maybe a small economical damage to the game developer). However, the same data faking strategies may be adopted in other domains.
Regulated applications such as the Digital Tachograph in road transportation and the Automatic Identification System (AIS) for vessel identification may suffer from faking attacks developed for the Pokemon Go and made popular through social media such as YouTube. Awareness and the possible deployment of rules for discouraging these types of cyber-attacks are important.
It is also important to change the conception of a GNSS receiver which has to be seen as a piece of a more complex puzzle. GNSS receivers are inserted in chains which do not end with the display of the user position. GNSS receivers are data providers and their information can, for example, be used by the on-board vehicle unit of the digital tachograph or by the AIS transmitter which will provide the vessel position to maritime authorities.
It is necessary to protect the full chain and not only the receiver input as traditionally done for jamming and spoofing attacks. Also the GNSS receiver output is vulnerable and has to be protected for example through authentication means.
The first steps towards the protection of a GNSS receiver (in its totality) are the “knowledge of the enemy” and the “fear for the unknown”. Jamming can be effectively mitigated only if jamming signals are properly characterized and modelled. Spoofing can be detected only if its impact on the receiver is properly known. GNSS data faking will be effective only if unexpected and underestimated.
When determining the threats we also have to keep in mind that “bad ideas move fast” and that forms of attacks can spread from one domain to another quite rapidly and sometimes in unexpected ways. For examples, several GNSS threats originated from other domains, mainly from the wireless communication sector. Thus, forms of attacks well known, for example, in the telecommunication sector should also be monitored. It is important to verify that other domains don’t become sources of inspiration.
This is the case of smart jamming which has been recently considered for disrupting the operations of a GNSS receiver. With respect to standard brute-force jamming, a smart jammer tries to operate without being detected and it does that by “hitting” where it hurts most. For example, jamming signals can be pulsed and interference may be generated only in correspondence of critical elements of the navigation message of the received GNSS signals. In this way, the receiver may be unable to recover the preamble of the navigation message or to decode important information.
A waste literature exists on smart jamming for wireless communications and sensor networks and concepts developed in these fields are (unfortunately) progressively percolating into the GNSS world. Since this “enemy” is still new to GNSS, a receiver may be unprepared with consequences on the applications depending on GNSS data.
The future of anti-jamming and GNSS cyber-security is probably to keep determining and characterizing the threats that may arise. Smart jamming has shown that there are components of the GNSS signal particularly vulnerable to time-localized interference events. GNSS cybersecurity will focus on protecting these components, enhancing the GNSS signal design, providing alternative sources of information, designing specific detection approaches which specifically monitor the weakest signal components. Attacks and defences will somehow progress in a parallel way, in a continuous quest for solutions to new problems.
One of the keys to defeating spoofing is to detect it in devices
 |
|
GPS jamming is a widespread phenomenon today. Spirent has deployed interference detectors in several countries globally and found interference in the GPS L1 band in every country a DETECTOR has been deployed in.
Often spoofing is seen as the exotic and purely theoretical cousin to jamming. But actually GPS spoofing beginning to emerge as being a very real and malicious threat. GPS spoofing involves a person or group broadcasting “fake” satellite signals to a GPS receiver to fool it into generating a false position and potentially following a false route.
While GPS spoofing is in its infancy compared with jamming, the wider use of time and location spoofing for malicious or misguided purposes has already started and there are several real, evidenced examples to back up the fact that GPS spoofing is becoming a threat as every bit real as RF interference.
Whilst spoofing has been referred to as a potential threat to GNSS and has been demonstrated several times in controlled environments (e.g. Todd Humphreys’ spoofing of a super-yacht in the Ionian Sea in 2013) it has often been regarded as being very difficult to conduct and requiring a high degree of expertise and GNSS knowledge.
• In August 2015, Huang and Yang from the Unicorn Team, Radio and Hardware Security Research presented a low cost GPS spoofing emulator at DefCon 23 in Las Vegas. Remarkably, they had no expertise in GNSS but found it easy to construct a low-cost signal emulator using Commercial off the Shelf Software Defined Radio and RF transmission equipment. The code needed for a GPS transmitter was freely available on the internet. They were able to spoof a car’s built in GPS Receiver in an underground car park, to spoof the date, time and location on two well-known brands of smart phone and to spoof a drone so that it would fly in a restricted area. Whilst the spoofing attack was relatively crude, none of the target devices were able to detect the attack or generate any warnings to the user.
• In December 2015 the Department of Homeland Security revealed that Drug Traffickers were attempting to spoof border drones as well as using GPS jamming equipment. http://www.defenseone.com/ technology/2015/12/DHSDrug- Traffickers-Spoofing- Border-Drones/124613/
• During 2016, with the release of the Pokemon Go Augmented Reality game, some hackers realised that they could sell gaming accounts to users who wanted to save time and effort capturing monsters. The hackers who sold these accounts faked their location in order to build up a large collection of captured monsters as quickly as possible without needing to visit real locations. The hackers spoofed their position at application level to start with – this required the operating system of their tablet or smartphone to be jail-broken, and software installed that provides fake location data to any application that uses GPS data. Whilst this worked well to start with, the main drawback of this system is that it is relatively easy to detect whether an operating system has been jailbroken and to then prevent devices with jailbroken operating systems from accessing the game. However, very quickly, hackers realised that they could easily build an RF signal generator to transmit replicated GPS signals. They did this using Software Defined Radio (SDR) programmed to act as a GPS transmitter. Some enterprising hackers even tried to sell their home made devices online to others who lacked the skills needed to build their own. What is very striking about events since 2013 is that the number of people with the specialist knowledge of GPS spoofing has risen from probably less than a hundred to (with Pokemon GO), tens of thousands, including many experienced hackers. This means that GPS spoofing is no longer a theoretical or improbable threat vector. Hackers have demonstrated that spoofing is not particularly difficult to accomplish and have used a wide variety of location spoofing techniques in order to cheat in augmented reality games.
Whilst it is true that spoofing is not happening on a widespread scale, it seems that it should be considered as a risk to the users of PNT-based navigation or timing systems in safety or liability critical applications. Systems that have been exposed to fake GNSS signals in addition to authentic ones, can often exhibit unexpected behaviour – this is perhaps not unsurprising as the presence of both replica and authentic satellite signals at similar power levels is not a usual test scenario. A spoofing attack does not always have to be successful in order to cause significant disruption in the targeted device or system and that is why testing against a realistic spoofing scenario is important. Mitigation to protect against spoofing attacks can range from relatively simple, inexpensive improvements to the use of sophisticated antenna technology that monitors the direction of arrival of the received signals but provides extremely high levels of protection against spoofing, or even the use of encrypted signals.
The military use encrypted GPS signals as protection against spoofing – only a user with the correct key can read the navigation data in the signals and a would be spoofer is not able to replicate the code. In Europe the Galileo constellation will offer the Public Regulated Service (PRS) which also uses encrypted signals to provide a high level of protection against GNSS signal spoofing – the PRS is intended to be made available to authorised governmental or military users.
One of the keys to defeating spoofing is to detect it in devices. There are ways to do this although there aren’t many receivers today that will warn a user if someone is attempting to spoof their GPS signals. For example a relatively simple detection mechanism would be to monitor the power levels of received signals – the power level of the spoofed signals is likely to be greater than that of the received signals. Monitoring relative signal strengths in the receiver would also work well – signals will have slowly changing power offsets… a sudden change might indicate a problem.
The important thing is to test PNT dependent systems and devices with a realistic spoofing scenario to see how they behave and to find out what can be done to improve their performance or to alert a user that there is a problem.
“Expect to have autonomous protection as a default feature in all GNSS receivers”
 |
|
The penetration of GNSS in different markets both professional and safety critical has risen concerns the last decade on its effective trustworthiness and robustness. Cybersecurity to date is known as everything that regards security including attacks and protection to computer, software and network systems. Attacks to radio signals have been known as signal intelligence, particularly in the defense sector. For GNSS, if the attention in the last decade has been mainly focused to radio frequency interference and vulnerabilities, the future will foresee a rising interest in cybersecurity, which includes the aspects of software, hardware and communication. In Qascom we call the combination of both as “Cybersecurity and intelligence”. This for example include futuristic GNSS attacks that target all elements of the Open Systems Interconnection (OSI) layers, from physical to data level, in order to achieve both deception or denial of service. This as a result has impact in the following subsystems:
• Attacks and vulnerabilities of the signals,
• Attacks and vulnerabilities of the software and hardware,
• Attacks and vulnerabilities of the data links;
While for software and hardware we can leverage from lessons and existing standards in computer and networks, attacks to signals are a new frontier: industries, researchers and government attempted to categorize attacks and define protections since many years. However, no clear plans and standards are available for cyber protection on signal attacks. No lifecycles have been defined at application and user level, such as operational centres that can analyze and detect new attacks and patch receivers and applications. Qascom is currently contributing to governments and standard organization to categorize attacks and define security metrics that can be used to build protection profiles and security targets for every application. It is likely that in few years and by 2020 all safety and financial critical user communities will have specific requirements for cyber intelligence protection and defense.
The other big challenge will be for the GNSS system providers: if protection at receiver level can be accomplished to date only with what we call “Heuristic techniques”, system providers are working to increase GNSS authentication and robustness at system level.
To better explain this concept, enabling protection at receiver level (such as antijam or anti-spoof) can be compared to an anti virus installed in a PC: it continuously monitor any upcoming attacks, and will alert and attempt protection if they arise. Protection at system level can be seen as the HTTPS connection with your bank. Regardless you have an antivirus or not, it will be hard for an attacker to eavesdrop the information that you transfer or to pretend to be the receiving party.
In this domain the new Galileo system is playing a leading role: Galileo has the capability to offer both an Open Service (OS) authentication and a Commercial Service (CS) authentication. These services are currently under design and testing, and Qascom has been a pioneer and one of the major players together with different partners. The Galileo OS authentication will provide initially protection of the navigation data, in order to verify that the data has been generated by the system. This is a fundamental step and very important from the legal perspective considering that to date any signal generator can produce any NAV data with any time in the past or in the future. The Galileo CS authentication will provide protection at code level, blocking the possibility for an attacker to generate a bogus PRN code. Qascom is also currently assessing for the European Commission the feasibility to provide authentication to EGNOS. Together with the Galileo authentication services, the use of the new Galileo modulations, larger bandwidth signals and use of multi frequency services will be a step forward for increasing robustness also.
As a conclusion, considering that both at receiver level and at system level with Galileo there has been a relevant progress in the last decade, we can expect to have autonomous protection coming as a default feature in all GNSS receivers in the next few years and full service protection at system level in the next decade.
As a vision for the future, and following the current scenario of the ICT security, the user will simply pay some fees or features for the cyber security and intelligence protection. He will sit down, relax, and enjoy positioning and navigation while in the background massive warfare scenario might happens including hostile jammers, spoofers or hackers.
Will we reach the 100% solution to GNSS trust and robustness? Absolutely not: security is the only business where the more we protect the more the attack increase, getting worse and worse during the years.












 (2 votes, average: 2.00 out of 5)
(2 votes, average: 2.00 out of 5)



Leave your response!